Introduction
The brand new disconnected period metric in AWS IoT System Defender now offers AWS IoT System Defender Detect clients the flexibility to watch Web of Issues (IoT) gadget connectivity standing and period of disconnection. Till now, clients needed to depend on customized self-managed options, utilizing AWS Lambda or Amazon CloudWatch, and Join/Disconnect occasion messages from AWS IoT Core occasion messages.
With the brand new disconnected period metric, clients can react to a tool disconnection primarily based on a specified disconnection interval threshold configured in AWS IoT System Defender. Monitoring this metric might help you perceive the well being of your fleet. Units which were disconnected for lengthy durations of time might have turn out to be weak attributable to not receiving updates and pose a safety threat, or now not work correctly when counting on different methods which have since developed. Clients also can apply disconnected period to beat many gadget fleet administration challenges, akin to transferring a tool that has been disconnect for an extended time period to a particular group of decommissioned or misplaced gadgets. In purposes the place distant property not often join, you possibly can apply this metric to outline whether or not a upkeep staff must be deployed to the situation or not. AWS IoT System Defender can be utilized along with AWS IoT System Administration, the place you should utilize fleet indexing to create queries that report which gadgets are disconnect and for the way lengthy. By figuring out the disconnected gadgets, you possibly can then outline dynamic teams or begin mitigation actions, addressing fleet administration necessities, in addition to safety compliance.
On this weblog submit, you’ll discover ways to configure a safety profile in AWS IoT System Defender utilizing the brand new disconnected period metric, and ship a message to Amazon Easy Notification Service (Amazon SNS) when a violation is detected. Additionally, you will use Amazon Easy Queue Service (Amazon SQS) to obtain and visualize the message from the SNS subject. Along with that, you’ll discover ways to question for gadgets which are in violation utilizing fleet indexing and the right way to create dynamic teams for these gadgets.
Overview
The structure diagram under, illustrates the movement of messages of the pattern resolution outlined on this weblog submit:
1- The simulated gadget connects after which disconnects.
2- After 5 minutes, the disconnected gadget will elevate an anomalous conduct alert on the safety profile.
3- The alert notification service will publish a message to the outlined SNS subject.
4- The SQS queue is subscribed to the SNS subject and it’ll obtain the message.
5- Utilizing a complicated fleet indexing search, you’ll return the issues underneath violation within the chosen safety profile.
6- From the search, you’ll then outline a dynamic factor group which is able to routinely index and group issues matching the search standards.
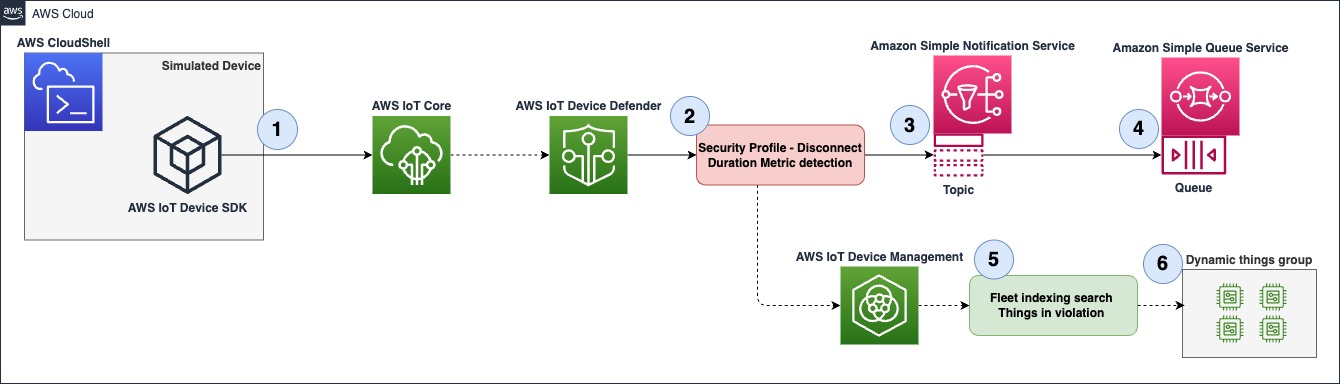
Determine 1 � Overview diagram
Conditions
- An AWS account with entry and permission to carry out motion on AWS IoT Core, AWS IoT System Defender and AWS IoT System Administration.
- AWS Identification and Entry administration (IAM) permission to create and assign roles in AWS IoT Core.
- AWS Identification and Entry administration (IAM) permission to create SNS matters and SQS queues.
- Entry to AWS CloudShell and primary information on Linux and AWS Command Line Interface (AWS CLI).
Walkthrough
Creating an SNS subject and an SQS subscription
Right here you’ll create the SNS subject and the SQS subscription for the subject the place the violation notification will get revealed to.
1- Go to SNS, then navigate to the left aspect menu, Choose Subjects then create a subject.
- Choose Commonplace.
- Identify � Disconnected_things_notification.
- Depart all different configurations as default and click on Create subject. Observe: You’ll use the default entry coverage that solely permits the subject proprietor to subscribe to it.
2- Go to SQS, then navigate to the left aspect menu, Choose Queues then create a queue.
- Choose Commonplace.
- Identify � Disconnect_thing_notification_queue.
- Depart all the opposite configurations as default, then click on Create queue. Observe: You’ll use the default entry coverage that solely permits messages from the queue proprietor.
Within the subsequent menu navigate all the way down to SNS subscription, then click on on Subscribe to Amazon SNS subject, selected Disconnected_things_notification, then save.
Making a safety profile
Subsequent you’ll create a safety profile which defines what is taken into account an anomalous conduct. You possibly can mix AWS IoT System Defender metrics, customized metrics and dimensions to be able to create an acceptable detection mannequin primarily based in your use case. Within the instance under, we are going to solely make the most of the brand new disconnected period metric, to study extra about how metrics will be mixed successfully, learn the safety use instances phase within the documentation.
1- Go to AWS IoT Core, then navigate to the left aspect menu, Choose Safety? Detect? Safety Profiles, Now click on on Create Safety Profile and choose Create Rule-based anomaly Detect profile.
2- Within the Specify safety profile properties menu configure the next:
- Identify � Disconnect_duration_5m
- Goal � A goal group, you possibly can choose a gaggle or a number of, on this instance you’ll be focusing on all registered issues.
- Function � Create a brand new position.
- Set SNS configuration, choose the beforehand created subject, Disconnected_things_notification.
- Within the SNS Function, choose create a brand new position.
- Click on Subsequent.
3- Within the Outline metric behaviors menu do the next:
- Underneath Cloud-side metricsSearch and choose Disconnect Period underneath Cloud-side metrics.
- Metric Habits � Choose Alert me.
- Habits identify � Disconnect_duration_5m.
- Within the logic fields, use Disconnect_duration is bigger than or equal � 5 minutes, which means any gadget which is disconnected for five minutes or extra shall be thought of anomalous.
- Click on Subsequent.
- Overview your configuration and click on on Create.
The determine under is an instance of what your metric conduct configuration will seem like.
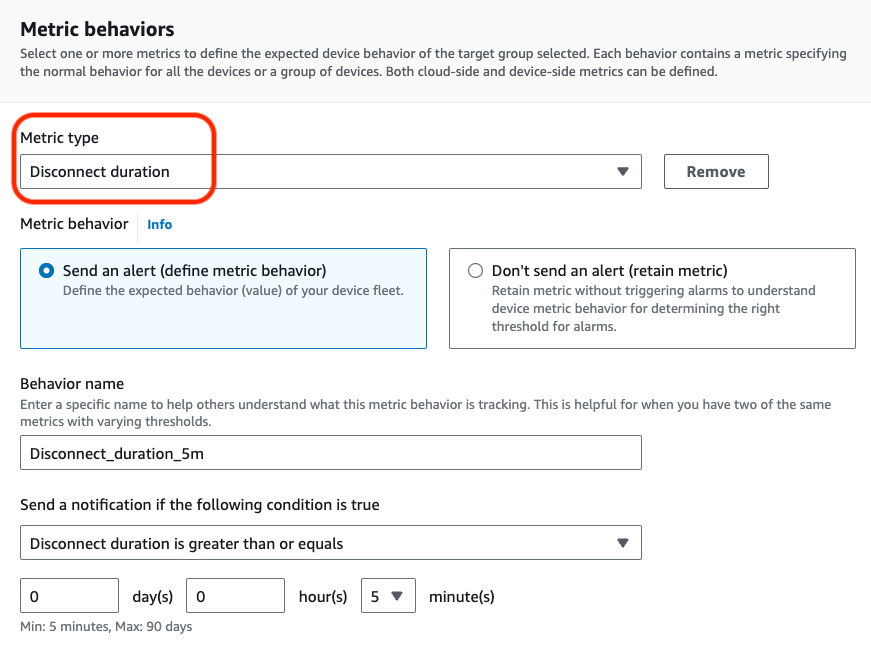
Determine 2 � Configure metric conduct menu
Simulating an anomalous gadget
1- First you’ll create an AWS IoT Core factor that shall be used to simulate a tool that has been disconnected for greater than 5 minutes and detected as anomalous by your safety profile.
Go to AWS IoT Core, then navigate to the left aspect menu, Choose Handle? All gadgets? Issues. Now click on on Create issues.
- Choose Create a single factor and click on Subsequent.
- Identify your factor test_thing, depart all the opposite configurations as default, then click on Subsequent.
- Choose Auto-generate a brand new certificates, then click on Subsequent.
- You may be prompted with the Insurance policies menu, if you happen to don�t have a coverage, create one with the next configuration:
{
"Model": "2012-10-17",
"Assertion": [
{
"Effect": "Allow",
"Action": "iot:Connect",
"Resource": "arn:aws:iot:<your-region>;:<your-account-id>:client/test_thing"
}
]
}- Navigate again to the earlier menu, refresh and fasten the created coverage, then Create factor. Obtain and save the personal key, public key and gadget certificates and click on completed, you’ll use these information on the next steps.
2- On this step you’ll be utilizing AWS CloudShell to put in and run a pattern utilizing the AWS IoT System SDK v2 for Python , nonetheless be happy to make use of some other AWS IoT System SDK and your most well-liked IDE platform.
Go to AWS CloudShell, as soon as the CLI has initialize, execute the next instructions:
python3 -m pip set up awsiotsdk
git clone https://github.com/aws/aws-iot-device-sdk-python-v2.git
3- Subsequent, add the personal key and gadget certificates that you simply downloaded when the AWS IoT core factor was created.
- On the highest proper, click on on the Actions menu, choose add information, choose the important thing file and add it, then repeat with the certificates file. Observe: the information are uploaded and positioned into the /house/cloudshell-user listing.
4 � Now you’ll begin the simulation by operating one of many pattern Python scripts.
From /house/cloudshell-user execute the next instructions:
aws iot describe-endpoint --endpoint-type iot:Knowledge-ATSPay attention to the endpoint worth, you want it within the subsequent step.
python3 ~/aws-iot-device-sdk-python-v2/samples/basic_connect.py --endpoint <your-iot-core-ats-endpoint> --cert <downloaded-cert-path> --key <downloaded-key-path> --client_id test_thingIf the pattern executes efficiently you will notice the next outputs:
Connecting to <your-iot-enpoint-here>-ats.iot.<your-region>.amazonaws.com with shopper ID �test_thing��
Linked!
Disconnecting�
Disconnected!
Confirming violation
After operating the simulation, you possibly can test if the violation has been detected by your safety profile. Observe that AWS IoT System Defender safety profiles might take a couple of minutes to publish a violation.
1- Now navigate to SQS, Choose Queues, and the queue you created within the earlier steps. Navigate to the highest proper menu and choose Ship and obtain messages, then on the Obtain message menu, Ballot for messages. You should have a message out there, and the physique will look just like the picture under, by utilizing this technique you possibly can combine AWS IoT System Defender violation alerts with a number of AWS Providers.
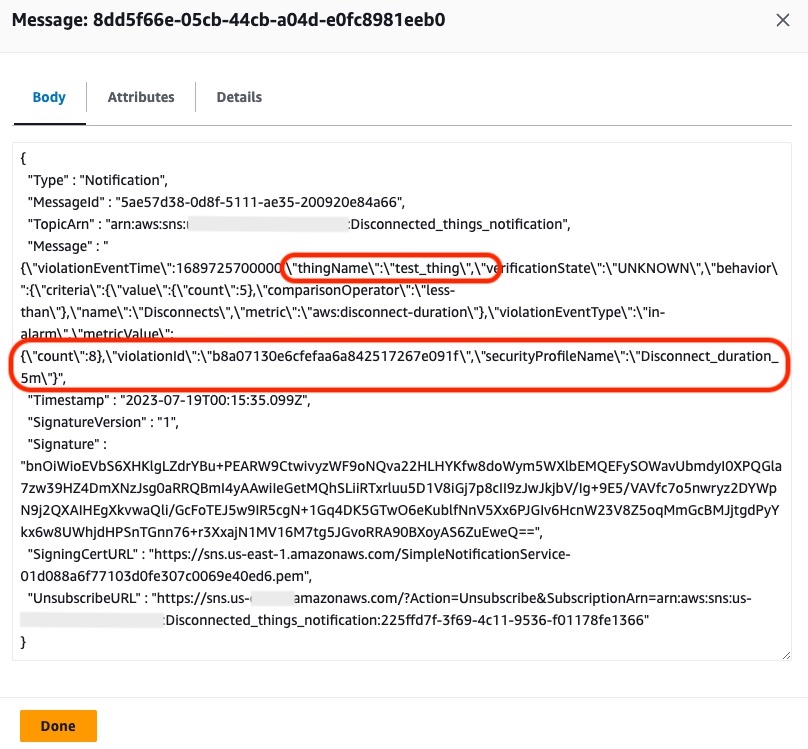
Determine 3- Violation notification message
2- You may as well visualize for the way lengthy an anomalous gadget has been disconnected. Go to AWS IoT Core, then navigate to the left aspect menu, Choose Handle? All gadgets ? Issues.
- Choose the factor you created within the earlier steps, test_thing.
- Navigate to Defender metrics underneath Metric, choose Disconnect Period.
You will note the same chart as under, indicating when and for the way lengthy your gadget has been disconnected. You should utilize the instructions from above to attach and disconnect your simulated gadget once more and observe how the reported metrics change. Have in mind the disconnect metric reviews in increments of 5 minutes, and isn’t up to date in actual time
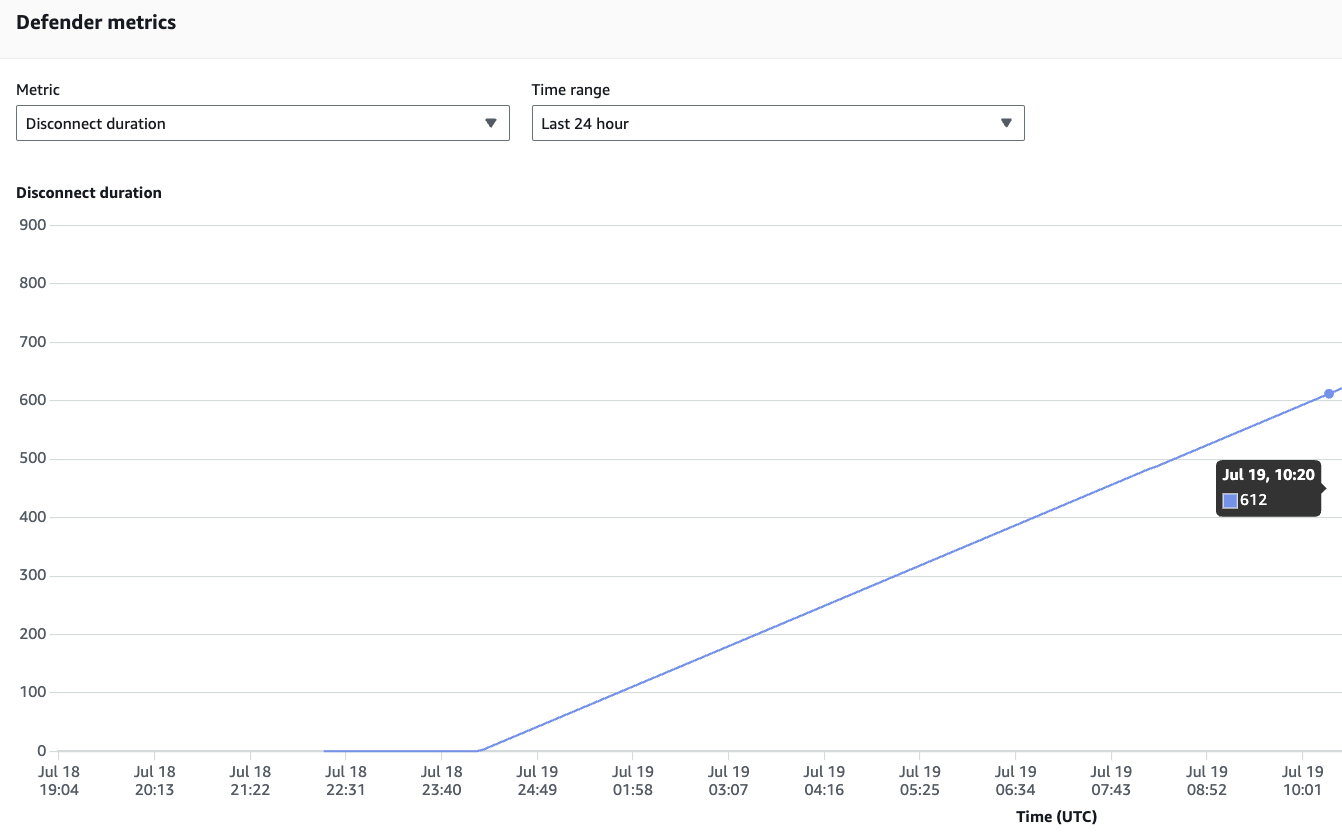
Determine 4 � Defender metric � disconnected period
The disconnected period metric can be out there by way of the list-metrics-values AWS CLI command. You should utilize the next command to question the metric:
STARTTIME=$(date -u +%Y-%m-%dTpercentH:%M:%SZ -d "5 minutes in the past")
ENDTIME=$(date -u +%Y-%m-%dTpercentH:%M:%SZ)
aws iot list-metric-values --thing-name test_thing --start-time $STARTTIME --end-time $ENDTIME --metric-name aws:disconnect-durationThe command will return an output with the newest metric replace, just like the instance under:
{
"metricDatumList": [
{
"timestamp": "2023-07-19T14:30:00+00:00",
"value": {
"count": 10
}
}
]
}Looking for gadgets in violation and creating dynamic teams
Earlier than you seek for a tool in violation, it’s essential to ensure Fleet indexing has been enabled for AWS IoT System Defender. To test that, go to AWS IoT Core, then navigate to the left aspect menu, choose Settings, navigate to Fleet indexing, click on on Handle indexing, within the new menu search and choose Add System Defender violations. The Fleet indexing service will begin indexing all values within the background, which could take a couple of minutes.
1- Go to AWS IoT Core, then navigate to the left aspect menu, Choose Handle? All gadgets? Issues.
- Click on on Superior search.
- Within the Question search subject use the next assertion: deviceDefender.Disconnect_duration_5m.*.inViolation:true
- This question will return all gadgets in violation underneath the Disconnect_duration_5m profile. In the event you adopted the walkthrough you will notice the your test_thing within the consequence record, as proven within the determine under.
- Now click on on Save question.
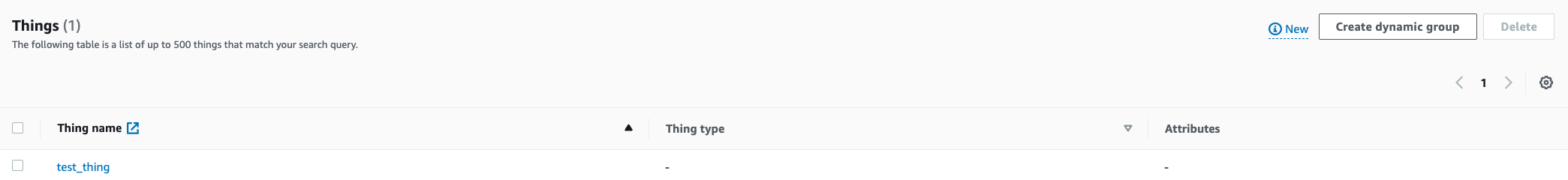
Determine 5 � Superior factor search consequence
2 � Go to AWS IoT Core, then navigate to the left aspect menu, Choose Handle? All gadgets ?Factor teams , then Create issues group:
- Choose Create dynamic.
- Factor group identify � Disconnected_things.
- Underneath Question, click on on Use saved question, then choose the saved question from the earlier step, deviceDefender.Disconnect_duration_5m.*.inViolation:true .
- Click on on Create factor group.
Inside a couple of seconds you will notice your factor as a part of the group, as proven within the determine under. By making use of dynamic grouping you possibly can remedy numerous use instances, for instance defining steady Jobs to the dynamic group will pressure updates to these gadget if they arrive again on-line, ensuring they’re compliant and updated. You may as well use dynamic group for fleet administration duties, as an illustration a tool which were disconnected for greater than 30 days will be deemed misplaced or decommissioned and added to a factor group which now not receives updates or denies join actions.
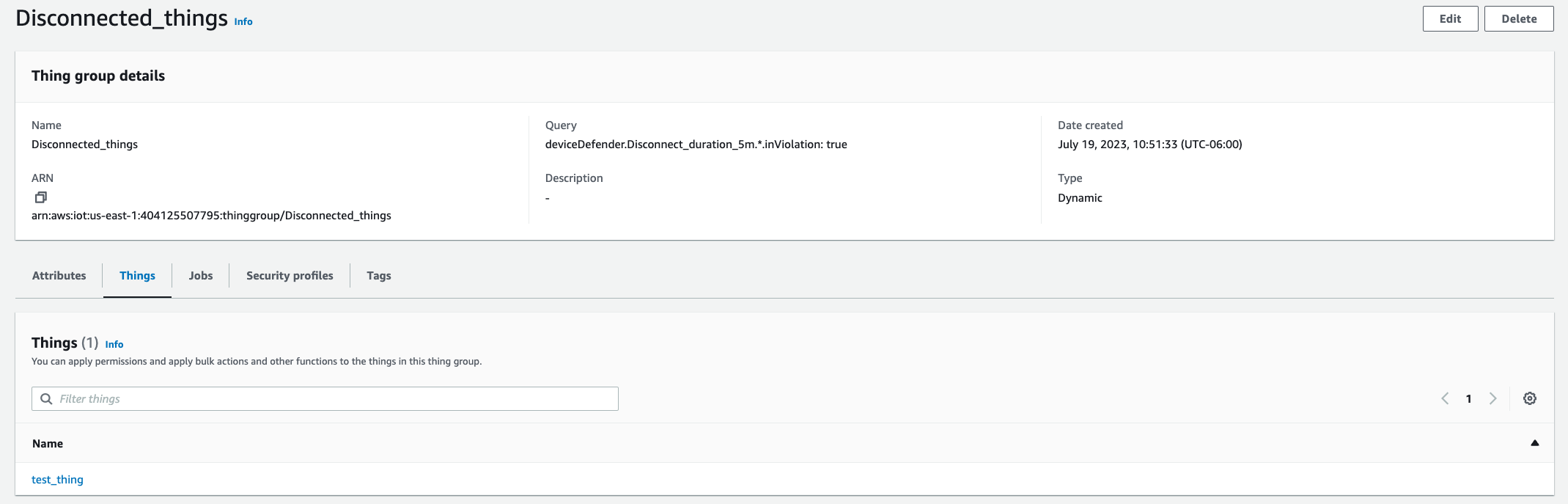
Determine 6 � Dynamic issues group
Clear up
With the intention to keep away from incurring value do the next:
- Delete the safety profile Disconnect_duration_5m.
- Delete the test_thing factor and its certificates.
- Delete the Disconnect_things group.
- Flip off System Defender violations in Fleet indexing.
- Delete each the SNS subject and SQS queue created in the course of the walkthrough.
Conclusion
On this submit, you discovered the right way to use the brand new AWS IoT System Defender disconnected period metric to watch gadgets with anomalous disconnection (or disconnect time) behaviors. You additionally discovered how this is applicable for safety and gadget administration use instances, and by utilizing the safety profile native integration with SNS, you possibly can create event-driven actions. Lastly, you used fleet indexing for search and dynamic grouping, and discovered how one can apply it for automated fleet actions and updates with Jobs. For a extra in-depth take a look at creating with AWS IoT System Defender, confer with this tutorial, Getting began with AWS IoT System Defender.
Concerning the Creator
Yuri Chamarelli �is an Amazon Internet Providers IoT specialist Resolution Architect primarily based out of Denver. As an IoT specialist, he focuses on serving to clients construct with AWS IoT and attain their enterprise outcomes. With a background on Controls engineering and over 10 years of expertise in IT/OT methods he has helped a number of clients with Industrial transformation and Industrial automation tasks all through many industries.
�is an Amazon Internet Providers IoT specialist Resolution Architect primarily based out of Denver. As an IoT specialist, he focuses on serving to clients construct with AWS IoT and attain their enterprise outcomes. With a background on Controls engineering and over 10 years of expertise in IT/OT methods he has helped a number of clients with Industrial transformation and Industrial automation tasks all through many industries.
�
�
�
�
 Andre Sacaguti is a Sr. Product Supervisor-Tech at AWS IoT. Andre focuses on constructing services and products that assist gadget makers, automotive producers, and IoT clients from numerous industries to watch and safe their gadgets from edge to cloud. Earlier than AWS, Andre constructed and launched IoT merchandise at T-Cell and Qualcomm.
Andre Sacaguti is a Sr. Product Supervisor-Tech at AWS IoT. Andre focuses on constructing services and products that assist gadget makers, automotive producers, and IoT clients from numerous industries to watch and safe their gadgets from edge to cloud. Earlier than AWS, Andre constructed and launched IoT merchandise at T-Cell and Qualcomm.

