Chinese language customers searching for reliable software program akin to Notepad++ and VNote on search engines like google and yahoo like Baidu are being focused with malicious adverts and bogus hyperlinks to distribute trojanized variations of the software program and finally deploy Geacon, a Golang-based implementation of Cobalt Strike.
“The malicious web site discovered within the notepad++ search is distributed by way of an commercial block,” Kaspersky researcher Sergey Puzan mentioned.
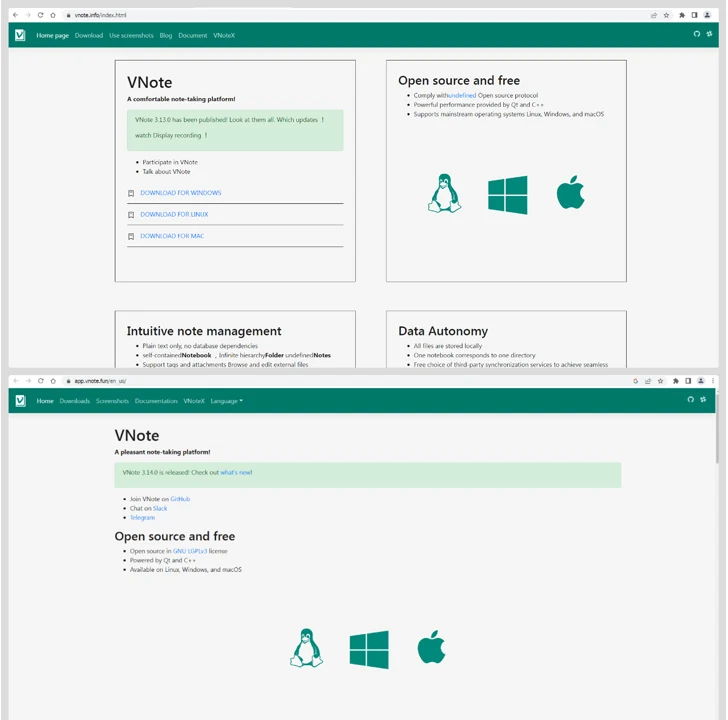
“Opening it, an attentive consumer will instantly discover an amusing inconsistency: the web site tackle incorporates the road vnote, the title presents a obtain of Notepad‐‐ (an analog of Notepad++, additionally distributed as open-source software program), whereas the picture proudly exhibits Notepad++. In actual fact, the packages downloaded from right here include Notepad‐‐.”
The web site, named vnote.fuwenkeji[.]cn, incorporates obtain hyperlinks to Home windows, Linux, and macOS variations of the software program, with the hyperlink to the Home windows variant pointing to the official Gitee repository containing the Notepad– installer (“Notepad–v2.10.0-plugin-Installer.exe”).
The Linux and macOS variations, then again, result in malicious set up packages hosted on vnote-1321786806.cos.ap-hongkong.myqcloud[.]com.
In a similar way, the faux look-alike web sites for VNote (“vnote[.]data” and “vnotepad[.]com”) result in the identical set of myqcloud[.]com hyperlinks, on this case, additionally pointing to a Home windows installer hosted on the area. That mentioned, the hyperlinks to the doubtless malicious variations of VNote are now not energetic.
An evaluation of the modified Notepad– installers reveals that they’re designed to retrieve a next-stage payload from a distant server, a backdoor that displays similarities with Geacon.
It is able to creating SSH connections, performing file operations, enumerating processes, accessing clipboard content material, executing information, importing and downloading information, taking screenshots, and even getting into into sleep mode. Command-and-control (C2) is facilitated by the use of HTTPS protocol.
The event comes as malvertising campaigns have additionally acted as a conduit for different malware akin to FakeBat (aka EugenLoader) malware with the assistance of MSIX installer information masquerading as Microsoft OneNote, Notion, and Trello.