The Dinner Social gathering Provide Chain Assault
A provide chain assault happens when a foul actor features entry to a corporation’s individuals and information by compromising a vendor or enterprise associate. Let’s consider this sort of assault as if it was a cocktail party. You invite your shut mates over and rent a catering firm that you recognize and belief to prepare dinner the meal. Nevertheless, neither you nor the caterer have been conscious that one of many waiters serving your company stole the important thing to your own home and made a replica. You throw a stunning celebration, and your mates rave in regards to the meals, and everybody goes house. However later that week you come house to seek out all of your valuables lacking.
To seek out out who broke into your property, you undergo the nanny cam you’ve gotten hidden in your baby’s stuffed animal. That’s once you spot the waiter roaming by way of your own home once you have been away. On this story, the caterer is the compromised hyperlink within the provide chain. Related to a cocktail party, firms must belief all individuals within the digital provide chain as a result of a threat to a provider can threat all the system — identical to one waiter exploited the belief between the caterer and the consumer.
Kinds of Provide Chain Assaults
Provide chain assaults might be understandably regarding for these answerable for cybersecurity inside a corporation. In response to Verizon’s 2024 Knowledge Breach Investigations Report, breaches resulting from provide chain assaults rose from 9% to fifteen%, a 68% year-over-year improve. Even in case you are diligent about defending all of your individuals, gadgets, functions, and networks, you’ve gotten little or no management or visibility into a foul actor attacking an exterior group.
There are completely different ways in which attackers can execute provide chain assaults. They’ll plant malicious {hardware} that’s shipped to clients. They’ll inject dangerous code into software program updates and packages which might be put in by unsuspecting customers. Or attackers can breach third-party companies, like a managed service supplier, or HVAC vendor, and use that entry to assault their clients.
The availability chain assaults that you simply see within the headlines are often those which might be slightly giant, and the sufferer group has little management over. Nevertheless, the extra frequent compromises occur when attackers first goal smaller firms (suppliers) with the purpose to get to their clients (actual targets). Let’s take into account the next instance of a regulation agency that results in a compromised consumer(s):

How the Consumer Safety Suite Secures Your Group
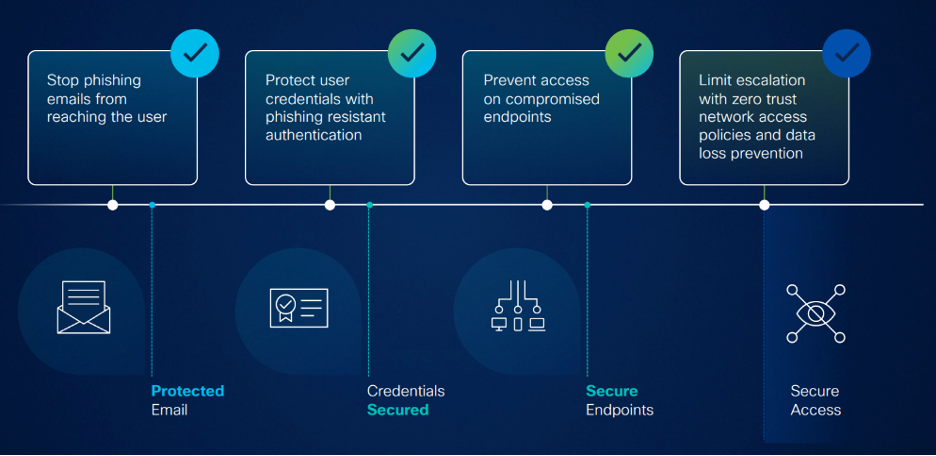
Cisco’s Consumer Safety Suite gives the breadth of protection your group must really feel assured which you could defend your customers and assets from provide chain assaults. The Consumer Suite gives e-mail and id safety, plus secure utility entry, all on a safe endpoint. Now let’s take into consideration how a provide chain assault can be prevented at key moments:
- E-mail Risk Protection: E-mail Risk Protection makes use of a number of Machine Studying fashions to detect malicious emails and block them from reaching the top person. If somebody in your provide chain is compromised and sends you an e-mail with a phishing hyperlink or malware, the subtle fashions will detect the menace and quarantine the e-mail. Even when the sender is listed as trusted, and the hooked up doc is one you’ve gotten seen earlier than.
- Cisco Duo: If a provide chain attacker will get entry to a corporation’s person credentials by way of compromising a vendor’s database, it is very important have multi-factor authentication in place. By pairing robust authentication strategies, like Passwordless, with Trusted Endpoint’s system coverage, your group can block unauthorized entry. And if there are potential weaknesses within the id posture, Duo’s Steady Id Safety gives cross-platform insights to reinforce visibility.
- Safe Entry: Safe Entry ensures that your customers safely entry each the web and personal functions. Safe Entry’ zero belief entry answer enforces least privilege entry, that means that customers are solely given entry to the assets they want. That implies that even when a provide chain associate is compromised, their entry to the community is proscribed and you’ll forestall lateral motion.
- Safe Endpoint: Safe Endpoint gives the instruments for organizations to cease and reply to threats. A kind of instruments contains Safe Malware Analytics, that sandboxes suspicious recordsdata and gives insights from Talos Risk Intelligence. Cisco evaluates 2,000 samples of malware per minute throughout all of Cisco’s merchandise to dam malware from reaching the top person. In instances the place an endpoint does change into contaminated in a provide chain assault, Safe Endpoint’s integration with Duo’s Trusted Endpoints mechanically blocks that person’s entry till the malware has been resolved.
The cybersecurity menace panorama might be overwhelming. There are various several types of assaults focusing on customers who simply need to deal with their job. Our purpose with the Consumer Safety Suite is to empower customers to be their best, with out worrying about breaches. Let customers get to work and we’ll deal with the safety dangers to guard your group from the highest threats.
To study extra about how the Consumer Safety Suite can defend your group at this time, see the Cisco Consumer Safety Suite webpage and join with an professional at this time.
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Linked with Cisco Safety on social!
Cisco Safety Social Channels
Share:

